This is Part Four of a Six-Part blog series on Cyber Risk Management from guest blogger Simon Goldstein.
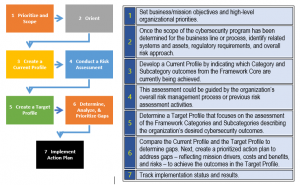
Every approach to risk management, cyber-oriented, operational, IT, financial, and so on covers the core basics NIST describes as Identify, Protect, Detect, Respond, and Recover. And there are also many ways to describe the performance operations needed to deliver those services. From an action perspective, NIST defines them through seven (7) steps:

Let’s look at each and see just how these provide some level of core function coverage.
Prioritize and Scope
Foundations define boundaries, establish level ground in uneven terrain, and secure the base upon which all else rests. Blueprints determine the nature of the foundation, and the structure, its functions, and features. These may infer construction sequences in accordance with regulations and accepted best practices. In terms of risk management practices, establishing business mission objectives may include determination of operational or organizational boundaries. These objectives also infer priorities across core practices, and should at least account for known vulnerabilities, available resources, stakeholder expectations, 3rd party obligations, and the practical threat landscape of operations across the proscribed areas of the organization.
Orient
In a cyber risk world, regulatory requirements, assets (hardware and software, and human capital too) plus funding and management resources must be aligned to objectives and scope, in the context of framework, to begin to shape an approach to addressing cyber risk. Currently, some firms take a compliance approach, focusing upon controls identified in regulatory or other frameworks, their presence, strength, and impact upon residual risk. Others may model threats, determine vulnerabilities and relate control or countermeasure actions to reduce risk experience and minimize recovery from successful adverse events. The choice may be made based upon operating practices of the enterprise, integration of risk management with internal or external audit, or other operating and financial risk management practices where control processes may create common ground for association. Where program scope is largely IT-centric, threat modeling and vulnerability assessment may lead the way. Regardless, this is a defining approach step that will impact assessment, gap analysis and remediation steps across the remainder of the program activities. It will also point to the specific content of descriptive risk terms, or taxonomy to be used to describe and operate within the risk management processes. If the cyber risk program is part of an overall integrated risk management approach, where information between cyber risk, audit, operations, and other areas is free to flow, a standard, shared taxonomy will be of immeasurable value.
Create a Current Profile
In other business process terms this is a “where we are” or “current state” determination step. What specific aspects of each core NIST Cyber Risk process are currently in place and operating with a known degree of reliability. This seems simple and straightforward. It may be. But it’s important to take a hard look at what’s being done in the current state, and to determine if processes achieve the intended outcomes. If they are, even if those outcomes are in need of enhancement, these should be incorporated into current state analysis. If not, a conservative approach would be where they are best discounted, since their current contribution to addressing cyber risk is not as intended. Drafts of this profile should be circulated to management and eventually vetted with the Executive Team to assure all perspectives of the company are incorporated in the current state profile. There’s an opportunity here to apply some integrated risk management (IRM) techniques by exploring audit findings, remediation tracking, and operational metric data to this process. This creates a more holistic result. Doing so promotes transparency and executive buy-in, while adding assurance complete data gathering and informed interpretation was thoughtfully and rigorously pursued. And, it will pay dividends in the steps to follow for identifying and evaluating gaps in a target state.
Conduct a Risk Assessment
We’ll not insert a written book here. If there is a risk assessment process already in place, this is the time to perform one to determine where significant inherent risk resides unchecked, where existing control practices or countermeasures are too weak to bring residual risk to levels acceptable to management, and where there are strong measures in place that must be preserved to sustain the current state and advance forward. If there is not one, this is the time to engage either a control or threat oriented approach to examine where the organization lies in terms of cyber risk exposure. Tools and methods abound to help organizations perform these, quantify inherent and residual risk, organize results according to adopted frameworks and regulatory obligations, and report findings to management at all affected stakeholder levels. In reporting, too often focus narrows to problem areas alone. That’s a mistake. It’s often overlooked but important to address what’s working well. Preserving achievements are vital to improvement. Ignoring or weakening them for the sake of vulnerable areas does not meaningfully improve the state of the whole or likely any of the program’s goals or objectives. This is where tool features that support distributed input, flexible but comprehensive reporting capabilities, easy to use interfaces, and simple workflows that can be configured to mirror established operating practices can deliver real value by minimizing participant effort necessary to thoughtfully attend to risk assessment.
Create a Target Profile
Some would counsel that this step could or should precede the risk assessment. Caution and a rational view of the organization need apply. On a scale of 1 to 5, where 5 represents the pinnacle of mature and comprehensive action, it’s unlikely any company’s true risk profile or threat footprint merits the investment of “all 5’s”. That’s the easy and frankly lazy way out of the task. The concept of risk appetite comes into play here. How much risk in any particular vector or category does management think is prudent and appropriate to accept? Decisions about risk appetite for particular kinds of risk, cyber security related, often express themselves in terms of impact upon reputation, operations, finances, or possibly regulatory compliance. These are executive management business decisions. Risk appetite is at the intersection of business and risk management. Risk cannot be eliminated. It must be managed through some action, either avoided, transferred, accepted, or mitigated. Ignoring it is a passive acceptance, in the reluctance to address it any further. Establishing target values for risk is defining a “future state” with regards to cyber risk for the enterprise or portions of the company in scope for the cyber risk management program.
Determine, Analyze, and Prioritize Gaps
Now that you know something about the delta between your current state and desired future state, the gap between them becomes clear. This is a straightforward exercise, at least in determining the relative extent of each gap. Determining what actions or opportunities there are to close the gaps is a more creative exercise. And strategies may apply more than one solution or approach to closing a particular gap. Some may have relevant controls strengthened in conjunction with some portion being transferred to cyber insurance coverage. Others may be mitigated by remediation projects, including user education. And still more may be dealt with by avoiding the source of risk, by eliminating some process or operation from the enterprise. Determining approach will help identify priority, resources (including hard costs), specific gains to be realized, and of course risks to successful achievement. Keep in mind sound risk management practices endure throughout cyber risk management efforts. Closing a gap to a $10,000 risk exposure with a $2,000,000 project makes questionable sense. What’s important here is to determine which gaps to close, in what sequence, by how much, by when, identifying what resources need to be assigned or reasonably acquired in the time proposed. To some extent management risk appetite will help determine priorities, and certainly approve plans and funding. Defining and stating the success state for each effort will be useful guides for gaining executive buy-in by articulating business value to be gained and lead to a greater understanding of the overall efforts of the cyber risk program.
Implement Action Plan
This is more than just arms and elbows heads-down work. Think about how you will communicate actions to the organization affected. What’s being done, why, the benefits to be gained by the company, how they will be affected, are all important matters to be shared along the way. Think about update and status reports. What metrics, what specifics can you report to demonstrate progress along the way? Sharing intermediary successes, finding opportunities, and acknowledging obstacles when they appear are all useful to engaging and incorporating stakeholders and interested parties into the program. Be sure to include timelines, milestones, resource plans, actual vs. budget expenses, issues and resolutions; all the basic project management best practices apply to these efforts. Implementation is also an opportunity to put integrated risk management processes into practice. Integrated risk management (IRM) will seek to incorporate content and actions from areas such as internal audit, operational monitoring, metrics from public relations and marketing. The idea is to get input and where relevant, metrics from these disciplines to demonstrate impacts on the organization by or as a result of efforts in the cyber risk management program. Reducing the risk of compromise of servers by increasing the timeliness of patching may have improved some metric on scheduling of carrier maintenance effectively making product distribution more reliable…just one example. Using audit findings and remediation status reports to validate progress on process changes to user education, leading to fewer cyber behavioral errors by staff identifying phishing emails, or password management in subsequent audits might be another example. The organization is a whole and integrating cyber risk management with other risk management and business functions leverages value from them all and creates a more complete information picture of the working of an organization.
Summary
These seven steps are not a one-time linear process, but describe one that’s continuous, cyclical and offers the opportunity for improvement with each cycle, leading to program and process maturity as well as greater control and understanding of the state an organization’s management of cyber risk. They are a guide, not a directive, and should be viewed as a roadmap for any venture into cyber risk as part of a comprehensive enterprise risk management program.

